Everything posted by AC_Martin_J
-
Please add remote access from a Chromebook Support
I'm using the android app to remote control devices from a Chromebook, but it's far from ideal.. I've noticed that it bypasses the MFA-login for instance, and the actual remote session is a bit difficult to use (you have to use two fingers on the touchpad in order to control a remote cursor). These are issues I was looking forward to see resolved with a web based remote control solution, but that doesn't seem to be in development. At least not for the time being. Here's a feature request I did about the web based solution: https://pulseway.featureupvote.com/suggestions/170678/web-based-remote-control
-
Q - Installing Pulseway during AutoPilot enrollment?
Thanks Mark G38! I'll look into that. As long as the client gets registered in pulseway (not just having the agent installed), then it should be fine.
-
Q - Installing Pulseway during AutoPilot enrollment?
Hi there! I haven't started using Microsofts AutoPilot (part of Intune MDM) yet, but I'm considering to do so in order to make the "out of the box"-experiences easier for both myself/IT and the end user. However, I don't want to hand over a new machine to one of our employees without knowing that Pulseway is installed and functional. I guess Intune can do some installations like the ones currently being handled by Pulseway, so some people may find this unnecessary, but we're currently managing as much as we can through pulseway (scripts, patch management, antivirus, remote control etc) and I'd like to keep it that way as much as possible while adding the benefits of AutoPilot. Do any of you have any experience deploying Pulseway with AutoPilot? Is it even possible at this point in time? // Martin
-
Operation refused as the account has 2FA enabled - options?
Sorry for hijacking the thread, but do you know if IT-Glue will allow integrations with this method once you guys have introduced it to Pulseway? That's the only thing preventing me from clicking the "Enforce MFA" button in Pulseway as it's currently configured with username+pass.
-
More Detailed Roadmap
Agreed! I'm sure Pulseway does some great development behind the scenes, but the current ways to let us know simply aren't working. You should consider regular updates along a predefined schedule, like publishing updates on day X once a month or on day X once every quarter, and then map a forum thread or webpage to it so we can get a better idea of what is coming and when.
-
Search and move Scripts
@Jamie Taylor - I can't see this change in our environment! We're using Pulseway OnPrem (8.7.3 build 709 release 307) and my experience is that OnPrem customers always have to wait several months (not weeks) for new updates. We still haven't benefitted from the 8.7.4 update that was published in july, and this is NOT a first time occurence. You guys need to improve the update workflow significantly, otherwise we'll have to move to another RMM provider. The development time frame for requested features in itself is extremely slow, and then having to wait even longer for the update to be applied is frankly ridiculous.
-
Message to multiple groups
I created a feature request on the featureupvote-page.. Hopefully it will get some traction and eventually an approval to start the development.. https://pulseway.featureupvote.com/suggestions/127787/send-messages-to-multiple-groups The issue with the idea Chris suggested is that the messages will be written ad-hoc and will not always be the same, so you'd have to modify the script and save it whenever you want to send a new message. That's why composing a message and then select which group/s to send it to inside the webGUI would be way easier. There's also no indication that the messages comes from Pulseway/IT-admin unless it's written explicitly within the message when using the msg method.
-
Anyone who has real use case of workflows or client portal?
Great stuff @Mark G38! I would've found the Client Portal a lot more useful if: 1 - The user was able to access it by right clicking the Pulseway-icon in the taskbar, rather than the current setup where we have to pre register accounts for that purpose and then give them permission to access the client portal through a browser. That's a lot of extra unnecessary steps and most certainly something that ordinary users doesn't want to get acquainted with. 2 - The newly added chat functionality is a great idea, but it does also require pre registration for those who want to use it. It's an administrative nightmare to add them separately, and as previously stated users will probably not see the benefits.
-
Windows Update problems - Feature Update
I'm echoing Kyle's question, as I'm also curious about documentation for this..
- Assets Overview report (WebApp) not displaying Mac computers
-
New Systems and Licensing
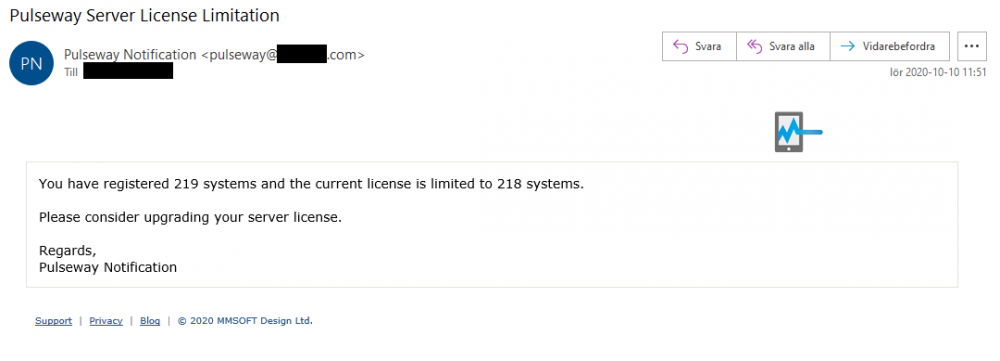
I have configured Email-notifications in our environment, and we receive notifications like these (see picture below) when we exceed the license limit. EDIT: Configured via Pulseway -> Server Admin -> Settings -> Email -> Server settings
-
Weboot site key manager
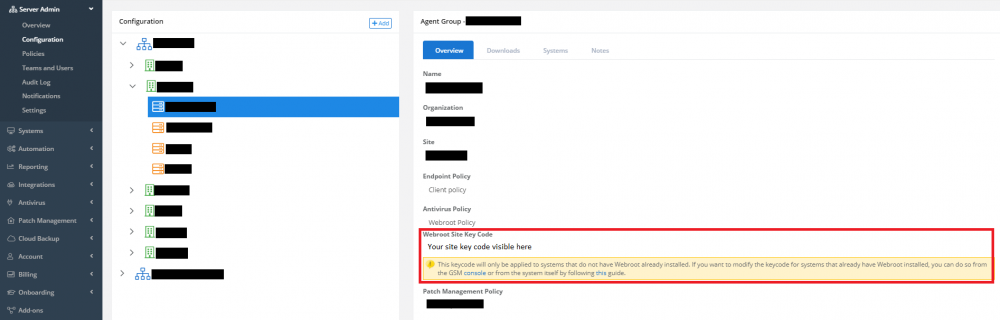
Hey guys! In case you're not already aware, I wanted to share a little trick that was recently added in Pulseway.. You can assign Site Key Codes to agent groups and let Pulseway automatically install Webroot on all clients that are added to that specific agent group. It has been working flawlessly for me and I don't have to copy/paste or worry about Webroot missing on any workstation or server. I also agree that fetching the key-codes from Webroot and show them (or at least show the webroot group name) in a drop down-menu would make it even easier to manage!
-
Asset info visible for offline systems
I noticed last week that they recently added a "Request feature"-button on the What's new tab in Pulseway.. It seems to be a voting-system where customers can upvote features they want/need, add comments and the Pulseway staff can also add different tags depending on development status etc.
-
Probe deployment for different IP Ranges/Subnets
I have installed a probe on a couple of computers+servers in our environment, and they only find clients within the same subnet. I'm able to ping devices in other subnets and access them with SMB-shares etc, but they are not found with a single probe.
-
Remote Desktop On Mac
It's available in version 8.4.0 now! I had to open Pulseway preferences on the machine and go into System -> Remote Control and enable it first. It's also necessary give the PulsewayAgent three different permissions within the security and integrity section of the system settings. I've tried it a few times and it seems to be working fine. The screen updates seems a bit sluggish but that might be because the machine is on wifi, and it's also in beta which may explain things. I love the fact that we are also able to transfer files back and forth. @Paul - Do you have any news to share if the enable remote control process on Mac will become easier further down the road? I'm more specifically thinking about enabling remote control on the agent using policies from the webGUI. Thanks, and well done implementing this!
-
Documentation for custom fields
This may not be entirely related, but I'd like the possibility to insert hostname in the email-notification that can be sent in an automation workflow.. Currently there is no easy way of knowing which computer the workflow was triggered on, except scrolling through the workflow history which might be a tedious task. I guess this could be achieved if we were able to insert custom fields like %pulseway.hostname% or whatever.
-
Services or Process - is not sending alert
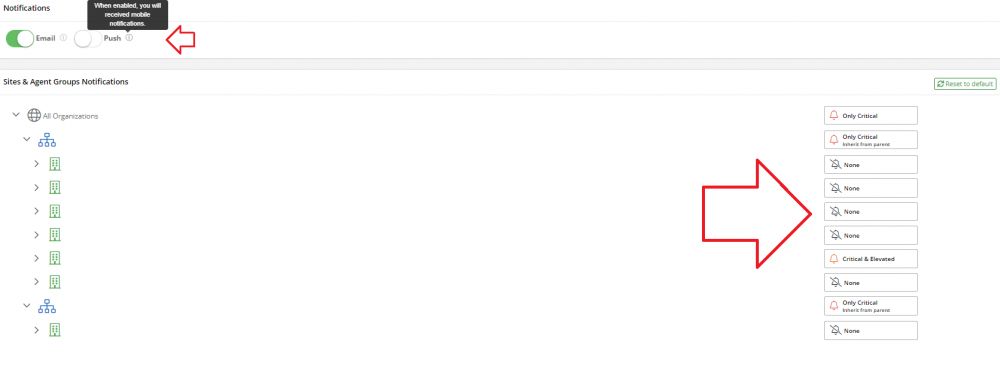
If you expect an email- or push notification to be sent whenever the monitored process or service is stopped, then you also need to enable notifications on your Pulseway user account before they will be sent. Login to Pulseway and open Account -> Notifications and make sure that you have enabled the corresponding notification level on either the organization or it's sub sites / groups. Also make sure either/or Email and Push are enabled at the top of that screen.
-
Workflows not running
I don't know why they set it up this way, but you need to enable the corresponding notification in order for the workflows to be triggered. I had the same issue with a workflow that was supposed to trigger when a system is back online, and I had to enable the policy setting: "Send a notification when the computer is offline" in order for it to work. I would imagine that you also need to enable "Send a notification when a user logs in with priority x" in order for your second workflow to work properly. Honestly, I think this implementation is stupid.. I like the idea of having workflows, but I hate the fact that we need to enable notifications because it also means that they will be sent via email if you have that setup in your environment. In my particular case, you can't adjust the notification priority so an email will be sent each time the system goes offline or online (quite frankly, I don't care, but the workflow task does in order to function).
-
ADD Printers
I'm distributing all of our printers via GPO instead.. That's been working flawlessly, so I don't see the needs of using PowerShell.
-
Uninstalling Solarwinds Products
Maybe this is helpful.. I ran this script in Pulseway to remove Solarwinds N-Central RMM a while back. It won't uninstall all the software solutions you mention, but it might put you one step closer if you replace some of the code with updated uninstall strings etc. $installstate = Get-Item -path 'HKLM:\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{940B905A-92ED-4646-B38B-321F80873C37}' -ErrorAction SilentlyContinue if ($installstate -eq $null) { Write-Host 'N-Central Uninstall Registry, was not found and might already be removed.' exit } else { Write-Host 'Uninstalling Ncentral RMM Agent' Start-Process MsiExec.exe '/X{940B905A-92ED-4646-B38B-321F80873C37} /qn' Start-Sleep -s 30 $program = 'Windows Agent' $program2 = 'Ncentral RMM Agent' Write-Host 'Verifying uninstallation...' $32bit = ((Get-ChildItem "HKLM:\Software\Microsoft\Windows\CurrentVersion\Uninstall") | Where-Object { $_.GetValue( "DisplayName" ) -like "*$program*" } ).Length -gt 0; $64bit = ((Get-ChildItem "HKLM:\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\Uninstall") | Where-Object { $_.GetValue( "DisplayName" ) -like "*$program*" } ).Length -gt 0; if ($32bit -eq $False -and $64bit -eq $False) { Write-Host "$program2 were uninstalled successfully." } Write-Host 'Deleting N-Central registry keys...' $Reg1 = Test-Path 'HKLM:\SOFTWARE\N-able Technologies' if ($Reg1 -eq $True) { Remove-Item 'HKLM:\SOFTWARE\N-able Technologies' -Recurse $Reg1v = Test-Path 'HKLM:\SOFTWARE\N-able Technologies' Write-Host 'Registry key 1 still present?' $Reg1v } else { Write-Host 'Registry key 1 did not exist and will be ignored.' } $Reg2 = Test-Path 'HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\N-able Technologies Inc. Windows Agent' if ($Reg2 -eq $True) { Remove-Item 'HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\N-able Technologies Inc. Windows Agent' -Recurse $Reg2v = Test-Path 'HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\N-able Technologies Inc. Windows Agent' Write-Host 'Registry key 2 still present?' $Reg2v } else { Write-Host 'Registry key 2 did not exist and will be ignored.' } $Reg3 = Test-Path 'HKLM:\SYSTEM\CurrentControlSet\Services\N-able Technologies Windows Agent' if ($Reg3 -eq $True) { Remove-Item 'HKLM:\SYSTEM\CurrentControlSet\Services\N-able Technologies Windows Agent' -Recurse $Reg3v = Test-Path 'HKLM:\SYSTEM\CurrentControlSet\Services\N-able Technologies Windows Agent' Write-Host 'Registry key 3 still present?' $Reg3v } else { Write-Host 'Registry key 3 did not exist and will be ignored.' } $Reg4 = Test-Path 'HKLM:\SYSTEM\CurrentControlSet\Services\N-able Technologies Windows Agent Maintenance' if ($Reg4 -eq $True) { Remove-Item 'HKLM:\SYSTEM\CurrentControlSet\Services\N-able Technologies Windows Agent Maintenance' -Recurse $Reg4v = Test-Path 'HKLM:\SYSTEM\CurrentControlSet\Services\N-able Technologies Windows Agent Maintenance' Write-Host 'Registry key 4 still present?' $Reg4v } else { Write-Host 'Registry key 4 did not exist and will be ignored.' } } start-sleep s 30 Remove-Item "C:\Program Files (x86)\N-able Technologies" -recurse $installstate2 = Get-Item -path 'HKLM:\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{940B905A-92ED-4646-B38B-321F80873C37}' -ErrorAction SilentlyContinue if ($installstate2 -eq $null) { Write-Host "$program2 was successfully uninstalled." exit }
-
SAML and Two Factor Authenticaion
Completely agree! Allthough the timeout can be lengthened now, it's still a big issue that we can't whitelist our browser. I turned on 2FA recently and I have to login to the WebGUI and Remote Control approximately twice a day. Extending the timeout even further doesn't seem like a good workaround. Also, please consider SAML-support, as mentioned earlier in this thread. We have ADFS and Smart Cards in our environment which we could then use to login to Pulseway.
-
Allow chat from Pulseway Remote Control App
According to the Pulseway Roadmap, Remote Control will be integrated within the WebGUI instead of a stand alone app. It is estimated to be released during Q2 2020. Hopefully we'll see that update arriving soon, and I imagine that it will become much easier to initiate chat messages and then remote control the user when everything is managed from the same place.
-
Create a local admin account
Unfortunately, Pulseway doesn't support Swedish characters within scripts at this point in time (I'd love to see that in the future though). However there's a way around it.. You can use ASCII-code instead of letters. I did this with a script recently in order to create a scheduled task, and it's working fine. Replace the following: $group = "Administrators" With: $group = [char]065+[char]100+[char]109+[char]105+[char]110+[char]105+[char]115+[char]116+[char]114+[char]097+[char]116+[char]246+[char]114+[char]101+[char]114 (The ASCII code above says Administratörer. Please note that putting the code within quotation marks will store the ASCII-code itself, which we don't want in this case)
-
Workflow - Allowing multiple instances of one trigger
Hi there! I think the workflows introduced in Pulseway 8.0 are powerful but not necessarily intuitive and easy to use.. My main concern is that you are only able to have one instance of a certain trigger enabled at once. For example "Service Stopped". I get the idea that you want to collect everything in one schematic, but it becomes problematic because you can't create branches directly under the trigger. Instead you have to add something like a condition first, and then create branches depending on the outcome, and then add multiple scenarios depending on what needs to be accomplished. In my case, I'd like to create a workflow where Service X is restarted on all workstations if it's found in a stopped state. At the same time as I want a notification when Service Y is in a stopped state on a specific machine. They are completely unrelated, but with the current configuration I somehow need to merge them in a single workflow. Trigger - Stopped state Condition - if service = X Action - Start service X Condition - if service = Y and machine = 1 Notify user via email Condition - if service not = X Condition - if service = Y and machine = 1 Notify user via email As you can see, one of the services (Y) needs to be added twice, simply because the machine may or may not fulfill the service X condition. This behavior will scale exponentially when I add more services to the mix. A better solution would be to either allow more workflows with the same trigger (and then maybe let the administrators decide in which order they will run), or let the administrator add branches directly below the trigger. In that case it could've looked something like this: Trigger - Stopped state Condition - if service = X Action - Start service X Re-evaluate workflow Condition - if service = Y and machine = 1 Notify user via email Re-evaluate workflow If no conditions are met, end workflow as successful One more thing.. Being able to get a preview of which machines will be affected when creating filters within the workflow would help a lot. A short list of 1-5 machines is enough to let the administrator know if the filter is misconfigured.
-
Android App Remote Control - Can't Login To Remote PCs
I'm getting suspicious about the keyboard-app being the culprit in this case, but I'm not an expert. I would at least consider using another keyboard app for a while to see if it behaves differently. I'm using Gboard on my OnePlus device and it works well with Pulseway Remote Control, another keyboard to consider might be "Switftkey" among others.
_a9c1b4.png)
_49ee3f.png)